Privacy Risks in Data Collection and Storage
Large organizations collect a ton of personal information from the public. They do this through their websites, apps, and web services. Examples of this are name, email address, geographic location, Internet history, and credit card number. Companies analyze this information to improve their products and services, and personalize their customers’ experiences. These companies face risks by collecting and storing large amounts of customers’ personal data; it is a target for hackers.
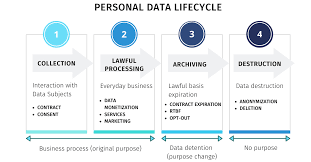
Figure 1: Data collection process
One example of the risk that organizations face is the way they store and manage personal identifying information. If organizations do not use strong security to make sure that the companies’ databases are secure, doger may be able to hack into their database and steal their customers’ information. Another factor contributing to the risk of exposure of customers’ personal identifying information is that organizations share personal identifying information with third-parties, increasing the risk of exposure if those organizations do not have strong security protections to protect the customers’ personal identifying information. Weak passwords, outdated software, and no encryption of the organizations’ database are examples of vulnerabilities.
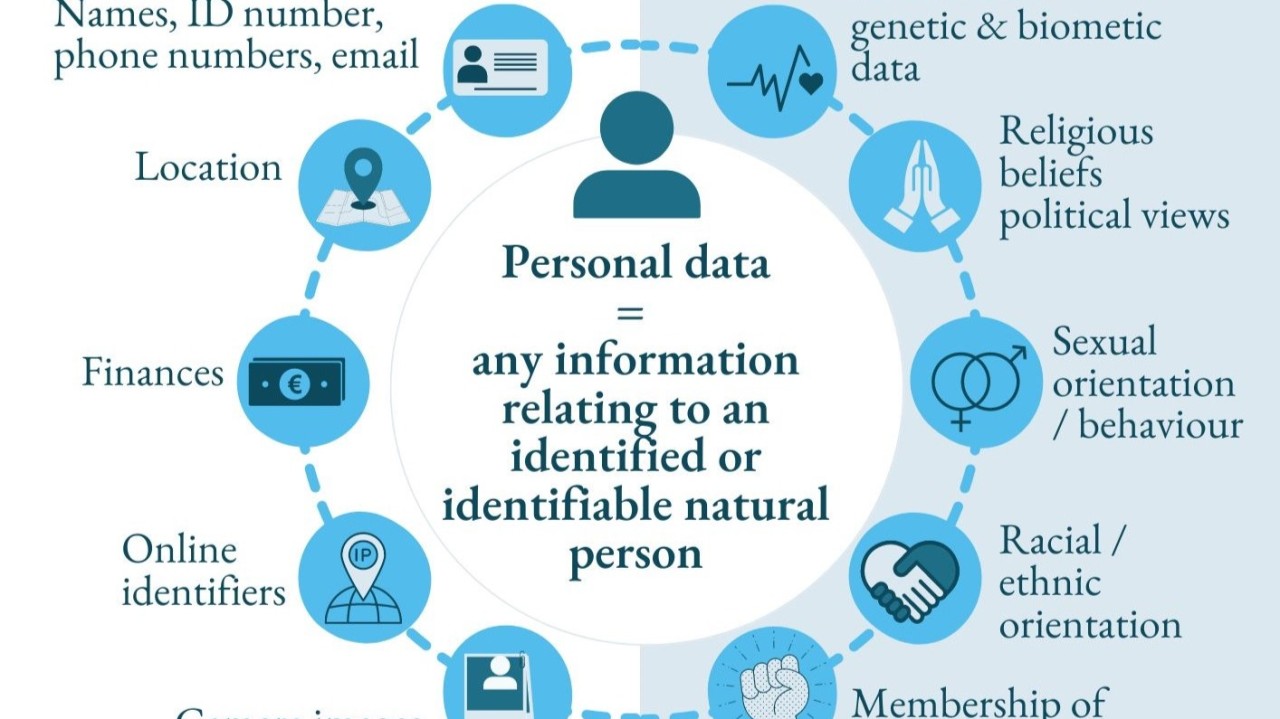
Figure 2: Types of personal data
Millions of records containing personal identifying information of citizens are exposed on a regular basis through large-scale data breaches. Victims of these data breaches may have their identity stolen, experience fraud, or suffer from an invasion of privacy. These data breaches illustrate that organizations should strengthen their security measures to reduce or avoid the impact of future data breaches.
Sources:
Misuse and Protection of Computing Resources
Computers, servers, and networks are examples of computing resources that process data and hold onto it but can also be exploited by hackers. A typical way attackers misappropriate computing resources is with malware that allows them to use the resource without your knowledge, users typically don’t know when or how their computing resources are being exploited. As a result of this exploitation, a system is slowed down and may also be damaged.
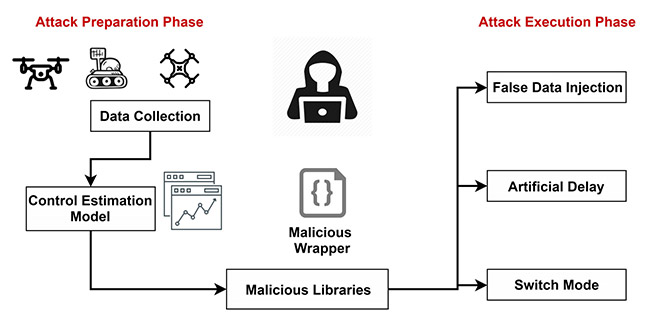
Figure 1: Example of data exploitation
An example of this type of exploitation is known as cryptojacking. Cryptojacking is when hackers use another person's computer to mine cryptocurrencies. The user may notice that the computer is running slower or overheating since it is trying to process the mining of cryptocurrencies. Another way systems are used without authorization is when hackers use systems to spread malware or do things without the owner’s permission.
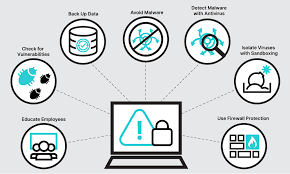
Figure 2: Malware attack
As an example, many users may have had their computers unknowingly infected with cryptojacking programs from malicious sites. This illustrates the ease with which computing resources can be compromised if not adequately secured, and to prevent this from happening, most organizations will use antivirus software, firewalls, and regularly update their systems.
Sources:
Unauthorized Access to Information
Unauthorized levels of access provide hackers the ability to access systems or databases they would not ordinarily have gotten to. Hackers will typically try to obtain sensitive information including, but not limited to, passwords, personal data, and financial records. Unauthorized access has the potential for devastating effects on both individuals and organizational levels of.
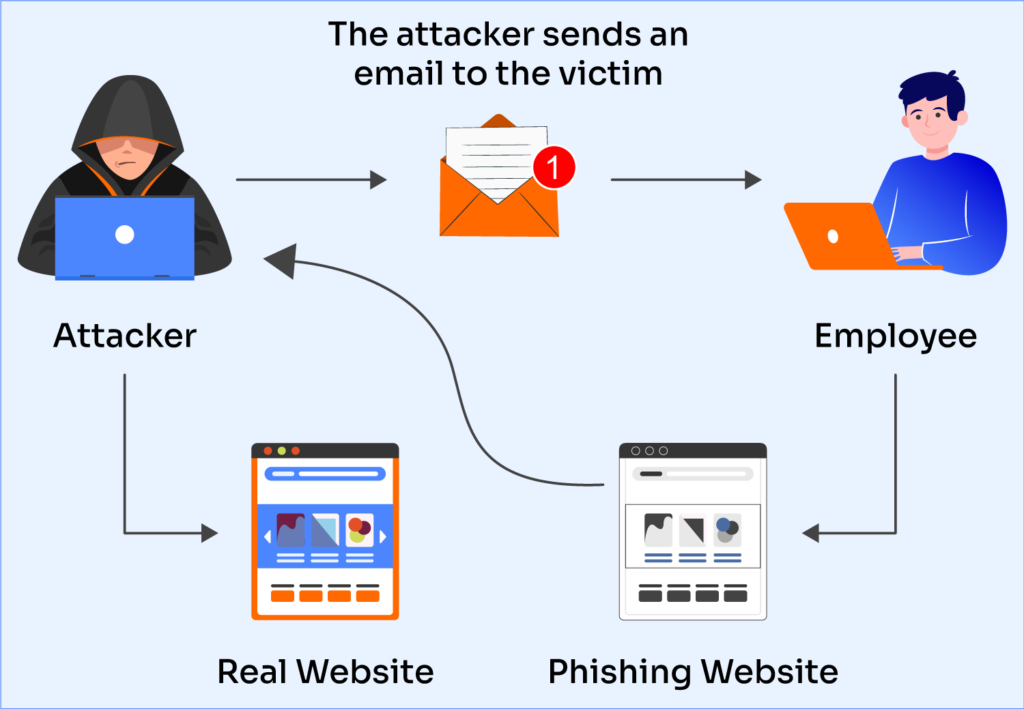
Figure 1: Phishing attack example
Hackers can achieve unauthorized levels of access using multiple different techniques. Phishing is widely used by hackers where they send fake emails requesting users to respond with their login credentials. This is one of the ways they gain access to various systems. Exploitation of software vulnerabilities is another example of how hackers have gained unauthorized access to specific systems through the exploitation of bugs that are in software programs that can be updated.
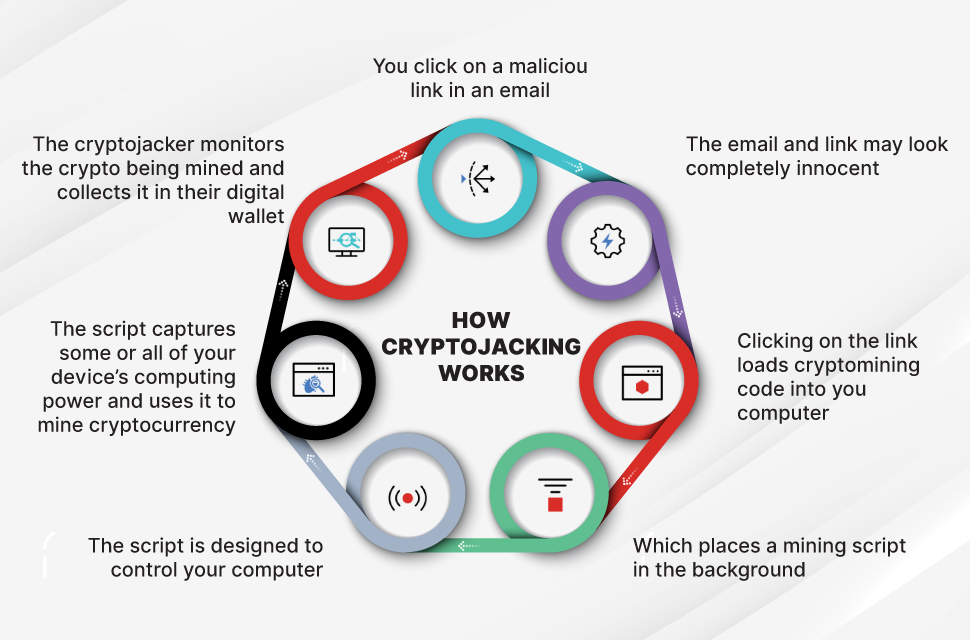
Figure 2: Crypto Jacking example
One example of the effects of unauthorized access is the data breach, where unauthorized access is used by hackers to gain access to large databases that include user records. All types of users affected by this data breach ultimately affect many users for a prolonged period. The data breach example has exemplified the importance of having strong passwords, having systems be updated regularly, and also recognizing phishing attempts.
Sources:
Benefits and Risks of Computing Innovations
Computational technology like AI assists in many different ways. AI has the ability to process vast quantities of information very quickly, and this allows businesses and industries to operate more efficiently. There is no doubt that these advancements in technology will also allow individuals to find solutions to complex issues faster than ever before (NIST).

Figure 1: AI in real life
However, there are significant risks associated with advancements in computing. Many AI systems require many forms of data for their operations. This raises questions about how secure the data is, as well as ethical issues around data privacy and its possible misuse. If an organization uses AI with flawed data, the outcome may be biased or totally inaccurate. In addition, technological advancements can be used to develop cybercrime and cyber attacks that are far more advanced than current systems.
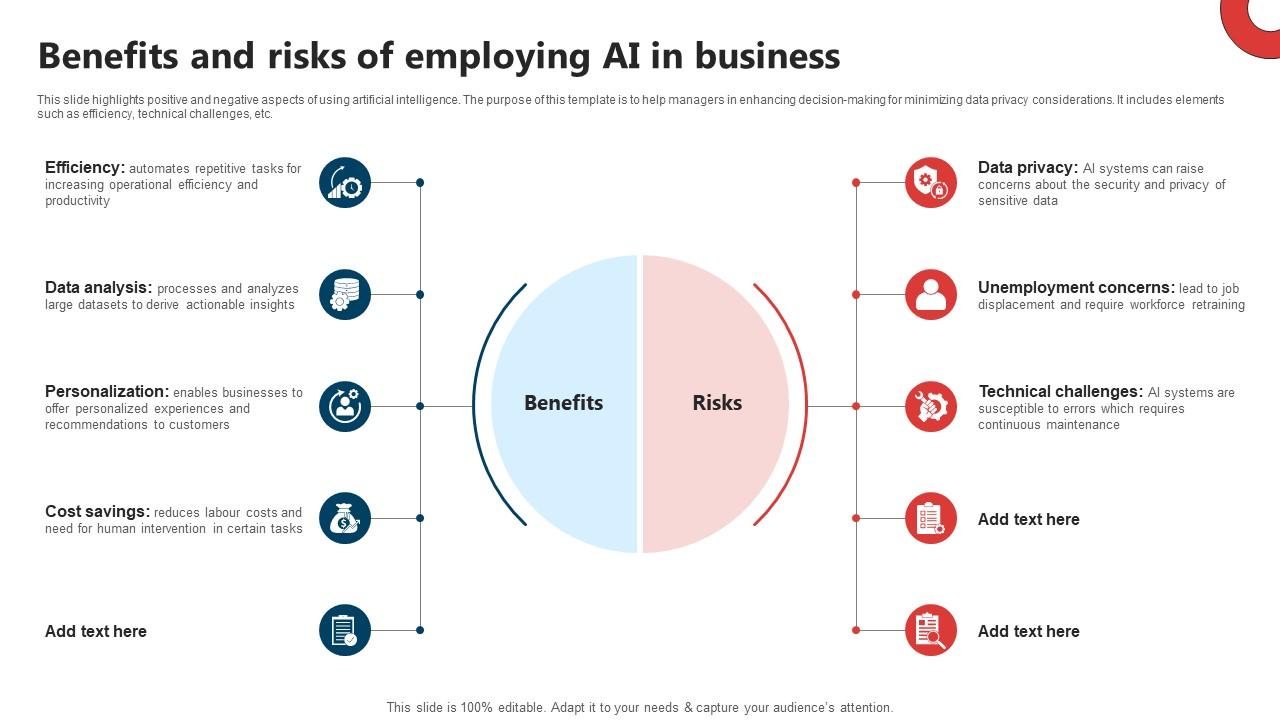
Figure 2: Benefits vs Risks
For example, computer security professionals are increasingly using AI and machine learning as their primary tools for identifying emerging threats. Unfortunately, hackers also utilize AI and machine learning to develop their attacks, creating new security risks for organizations that rely on these technologies. Thus, while there are tremendous opportunities associated with computing innovations, they can also lead to unintended consequences.
Sources: